Virtual Attack
By Jason Miks
Viruses, spam, hackers, phishing—words that are increasingly familiar yet businesses here are still dangerously behind the times. Jason Miks writes...
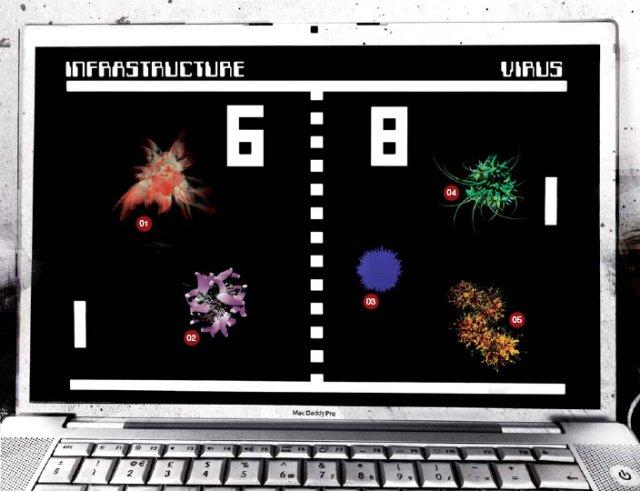 01 Spam, 02 Spyware, 03 Phishing, 04 Viruses, 05 Trojans. Computer threat images courtesy of MessageLabs. These images have been created using unique code from each threat. Illustration by Phillip Couzens.
01 Spam, 02 Spyware, 03 Phishing, 04 Viruses, 05 Trojans. Computer threat images courtesy of MessageLabs. These images have been created using unique code from each threat. Illustration by Phillip Couzens.
The government and Yahoo Japan have one thing in common: both are major organizations with intricate security systems, yet they had left themselves open to some of the worst attacks of our modern age—cyber terrorism.
In an ugly office block in Nagatacho, Tokyo, sits the nerve center of the Japanese government’s attempts to coordinate the country’s information security efforts. Established in 2005 in response to a series of cyber attacks on government Websites, the NISC acts as a point of contact between government bodies, businesses and individuals, and also coordinates with relevant organizations overseas.
Although much of the center’s work focuses on boosting cyber preparedness for critical infrastructure, the center is also trying to improve cooperation with the private sector. “We’re not trying to scare people over the probability of cyber attacks and cyber terrorism,” says Masayuki Ogata, deputy counselor of the NISC, Cabinet Secretariat. “We’re trying to take a more pragmatic approach by enhancing public-private partnerships. We hold cross-sectoral exercises and invite representatives from all sectors.”
A reminder of the challenges Japanese firms face in protecting against these attacks came in late September, with the Yomiuri Shimbun reporting that Yahoo Japan Corp.’s auction site had been accessed illegally about 1.5 million times since May through the use of passwords and codes stolen from the site’s members. This information was then used to allow fake designer goods to be sold under different users’ names.
Gene Endo, who manages Fortify Software’s Japan operations, says the damage done by data theft to companies such as Yahoo is not limited to the data loss itself. “It reflects on their reputation too,” says Endo.
Despite the problems at Yahoo, Seiji Yamamoto, Japan sales director of MessageLabs, believes large corporations based in Japan are generally better prepared than their smaller counterparts. “Global businesses know about the risks and are more aware than small and medium sized businesses,” he claims, though he warns that awareness overall is still not as high as it should be. “Most Japanese companies are not feeling that there are risks,” he says. “Many have not suffered problems, so they might know about them but they won’t pay for security.”
Cyber crime—high profits and low risk?
According to the Japan Computer Emergency Response Team Coordination Center (JPCERT/CC), a nonprofit organization that acts as a point of contact between other Computer Security Incident Response Teams (CSIRTs) around Japan, the threats to these companies are coming increasingly from those hoping to profit illegally. “In the past, online attackers like script kiddies (inexperienced malicious hackers) were motivated by others’ reaction to their escapades,” says JPCERT/CC spokesperson Yoko Kohda. “As it is now, the Internet has allowed attacks with the promise of higher profits and low risk of arrest [and] an underground market selling tools to commit such crimes has emerged,” she says, adding that this type of crime is moving from individual perpetrators to criminal organizations.
Indeed, the growing problem of coordination was highlighted in September, when the National Police Agency reported an 84 percent jump in reports on “harmful” Websites to its Internet hotline center, including the sale of illegally acquired bank account details to third parties.
JPCERT/CC was established in 1992, and has since been gathering information on computer incidents, issuing security alerts and providing incident responses. “[Our] objective is to raise the cost and risk to the attackers,” Kohda says. In the second quarter of this year, JPCERT/CC received a total of 734 incident reports, with some problems such as phishing showing big falls from their 2007 highs. “Recently, the number of incident reports sent to JPCERT/ CC has slightly declined and certain types of incident trends show a decline,” Kohda says. “This is because viruses with large outbreaks like Code Red have decreased in number. In their place, however, malware and bots have significantly increased over the past few years.”
Spam attack and internal breaches
Yamamoto says that denial-of-service-attacks, or DoS (an attempt to make a computer resource unavailable to its intended users) including those in which email servers are overloaded with spam, have become an increasing problem, with the share of spam in all email traffic to companies rising rapidly over the past three years.
According to a MessageLabs report in September, the spam rate in Japan so far this year is almost 70 percent, up from the 60 percent rate last year and 50 percent in 2006. He says construction company Kajima was particularly hit hard last October by a DoS attack that jammed its email system with 4 million spam messages a day.
However, Endo points out the threats to a firm’s information security can often also originate from within. “Most companies feel their internal systems are safe because they’re not facing outside. But large corporations such as Sony have had internal data breaches,” he says.
The key is education
Nicolas Christin, associate director at Carnegie Mellon University’s Networking Institute, says such leakages often follow quite a mundane route, such as a company employee deciding to bring their laptop home. The laptop ends up getting infected with a virus and customer or user data is then compromised. “This isn’t hypothetical” Christin says. He believes the key is education and raising awareness among corporations and users. “Education is of paramount importance. Once private information is gone, you can’t get it back. But what you can do is educate people so they are secure…Corporations need to train employees and the government should invest in education,” he says.
Pauline Reich, founder and executive director of the Asia-Pacific Cyber Law, Cyber Crime and Internet Security Research Institute in Tokyo, believes there is significant scope for Japan to improve its cyber security education, including at the nation’s universities. “The problem with Japanese higher education is that there is very little interdisciplinary study or collaboration between the faculties,” Reich says. “Another is that the world has changed since a lot of people went to university. So there’s a need for in-service training, continuing education—in the computer fields, or in engineering or in law—in an interdisciplinary manner.”
Reich also believes Japan needs to look overseas if it wants to keep up with evolving threats. “Universities need to have foreign professors coming to visit. You need to stay up to speed by having the contact with people outside Japan.”
Although retraining employees may come at a cost, the price of a security risk far outweighs the price of making sure that customers, corporations and staff are properly protected from malicious attacks. As we move more and more towards electronic infrastructure, Japan Inc cannot remain complacent when it comes to ensuring that the necessary security measures have been taken—both through the cables as well as the gates.





